TCP vs UDP
Getting computers to talk to each other is a crucial element to productivity. The days of yore brought us “sneakernet” and set the stage for the internet technology stack that we know and tolerate today. The reliability of inter and intra-system communication hit many milestones over the years. Initially, bandwidth was the primary bottleneck for applications and communications (2400 baud anyone?) so as interfaces and compute horsepower increased, the applications had no problem finding ways to use up the bandwidth as soon as it was provisioned.
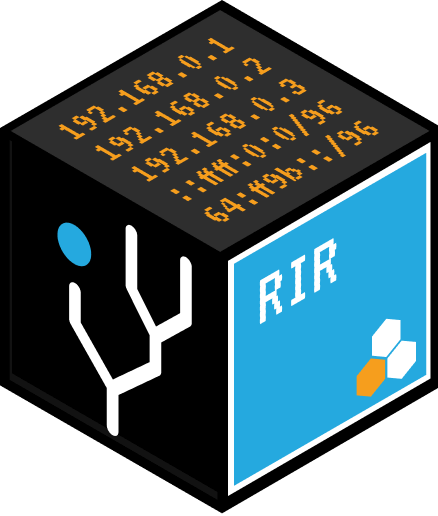
One of the important mechanisms that enable communication is the Internet protocol suite. Both TCP and UDP belong to the transport layer that transfers data to applications and insulates them from unwanted interference. While both protocols have the concept of ports, they work in very different ways.
The TCP protocol provides a highly reliable, ordered, and error-checked delivery of byte streams between two applications. It is the most common networking protocol used online and establishes a connection by using a three-way handshake.

Packet handshakes in action.
TCP is used when all data must stay intact when transmitting and receiving between devices. As a result, the TCP protocol has a relatively high overhead and is harder to implement. It also requires more advanced hardware and system services while not supporting broadcast communication. TCP protocol can be compared to a conversation between two people. Since both people need to communicate with each other to establish a connection and transmit data.
The UDP protocol is connectionless. It provides minimal data integrity by calculating and comparing checksums but exposes the user to all other network events including lost, duplicate, and out-of-order messages. The simplicity of this protocol makes it suitable where speed rather than integrity and error correction is preferred. This includes real-time applications, video streaming, and multiplayer games. It works well with boot loaders and serves as a basis for the TFTP protocol. The UDP protocol can be compared to a person speaking outside with a megaphone. Most people in the surrounding area who are listening to the speaker will be able to hear just about everything being communicated, however, there’s a possibility that some people may not be listening or hear anything at all. This is because the UDP protocol does not guarantee that all data will be successfully transmitted.
These protocols serve different purposes, but some key differences to remember are that a TCP protocol is connection-oriented, provides error checking, and because of this, is heavy-weight. While a UDP protocol is connectionless, has a faster speed, and is lightweight. So whether a reliable connection for tasks such as sending an email or streaming a live video is needed, there’s a suitable protocol for that.